More Power. Better Compliance. Smarter Print Designs | OnPrintShop v13.0 is Live - Learn More
Solution Security
We are committed to protecting our customers from security threats and incidents. At OnPrintShop, we follow security by design and comply with the highest standard of ISMS with ISO 27001:2022 certification underlining our leadership in protecting sensitive information assets.

Protecting Your Data
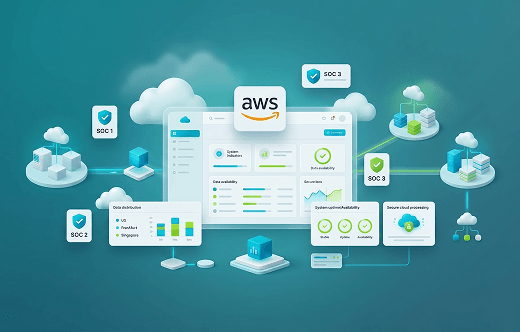
Hosted By Amazon Web Services (AWS)
- AWS data center is SOC 1, SOC 2, and SOC 3 compliant. All data is stored and processed in multiple AWS zones based on customer’s locations.
- Mainly available zones are in US, Frankfort, and Singapore regions.
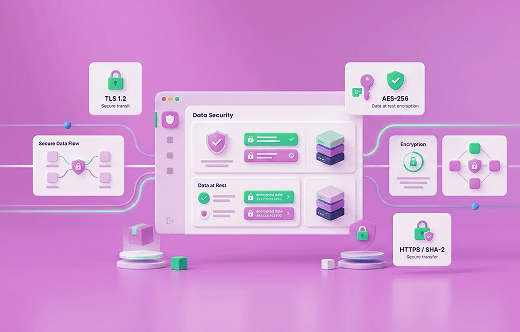
Data Security During Transit & At Rest
- All data in transit are encrypted using secure TLS cryptographic protocols. (TLS 1.2)
- All data at rest are encrypted using Advanced Encryption Standard (AES) with a 256-bit key.
- All data transferred over HTTPS are encrypted using SHA-2 compliant cipher suites.
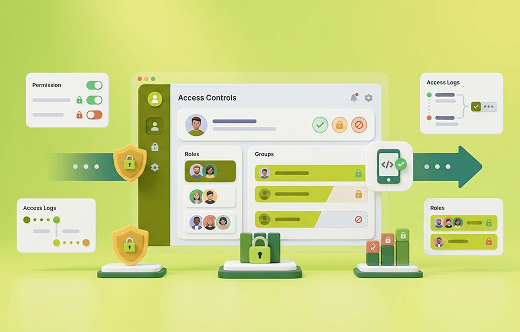
Access Controls
- Role-based access through IAM enforces segregation of duties, two-factor authentication, and end-to-end audit trails, ensuring access in accordance with the security context.
AICPA SOC 2 Certified
- With SOC 2 standards, we help our clients to strengthen their data security architecture and abide by exemplary compliance standards.
Malware & Spam Protection
- Period manual and automated security reviews and risk assessment.
- Real-time threat detection and blocking to prevent malware, phishing, and spam attacks.
ISO 27001:2022, ISO 9001:2015 Certified
OnPrintShop's certification of ISO 9001:2015 and ISO/IEC 27001:2022, affirms our dedication to quality and secure Web2Print solutions for global print businesses.
Access Control and Organizational Security
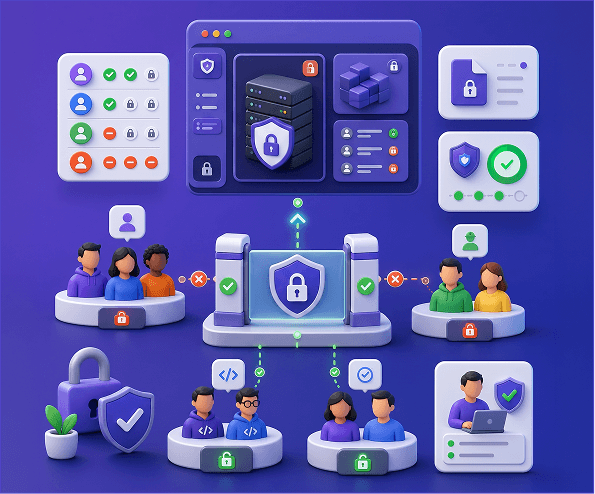
Segregation Levels

AWS Resource Level
Data is segmented across databases and S3 buckets based on customer and data type. Each dataset is logically isolated across accounts, with access secured through strong authentication and authorization controls.

Network Level
Dedicated VPCs are created for each environment, with production fully isolated from development and other environments to ensure strict network separation.

Application Level
Customers are logically segmented at the application layer, ensuring that data access, workflows, and user roles remain isolated across accounts within the platform.

Tenant Level
Built on a secure multi-tenant architecture, where infrastructure is shared but customer data remains fully isolated and protected through strict access controls.
PCI DSS Compliance
Application Security
Network Security
Physical Security
We segregate access to our data at different levels:

Data Center
OnPrintShop is hosted on Amazon Web Services (AWS) and guarantees the implementation of measures according to the red security level. Cloud service providers operate state-of-the-art data centers that focus on security and protection of data as the primary design criteria. This is demonstrated by ISO/IEC 27001 certificate.

Offices
The access to offices is restricted and monitored by the reception who are also responsible for visitor management. According to the security zone concept, some areas are locked, and visitors must be guided by employees.
Data Backup & Recovery